Network security professionals often assume IP geolocation delivers precise coordinates, yet most implementations struggle with accuracy ranges exceeding 50 kilometres. Understanding geolocation accuracy transforms how you interpret security alerts, validate access requests, and detect threats. This guide clarifies what geolocation accuracy truly means, explores the technical factors affecting precision, compares IP-based versus GPS methods, and demonstrates practical applications for enhancing your cybersecurity posture and IP management strategies in 2026.
Table of Contents
- What Is Geolocation Accuracy?
- Comparing IP-Based And GPS Geolocation Accuracy
- Challenges And Limitations Of Geolocation Accuracy In Network Security
- Practical Applications Of Geolocation Accuracy For It And Security Specialists
- Explore Instant IP Lookup Tools For Geolocation Accuracy
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Definition and measurement | Geolocation accuracy measures how precisely digital methods determine geographic location, typically expressed as error margins in kilometres |
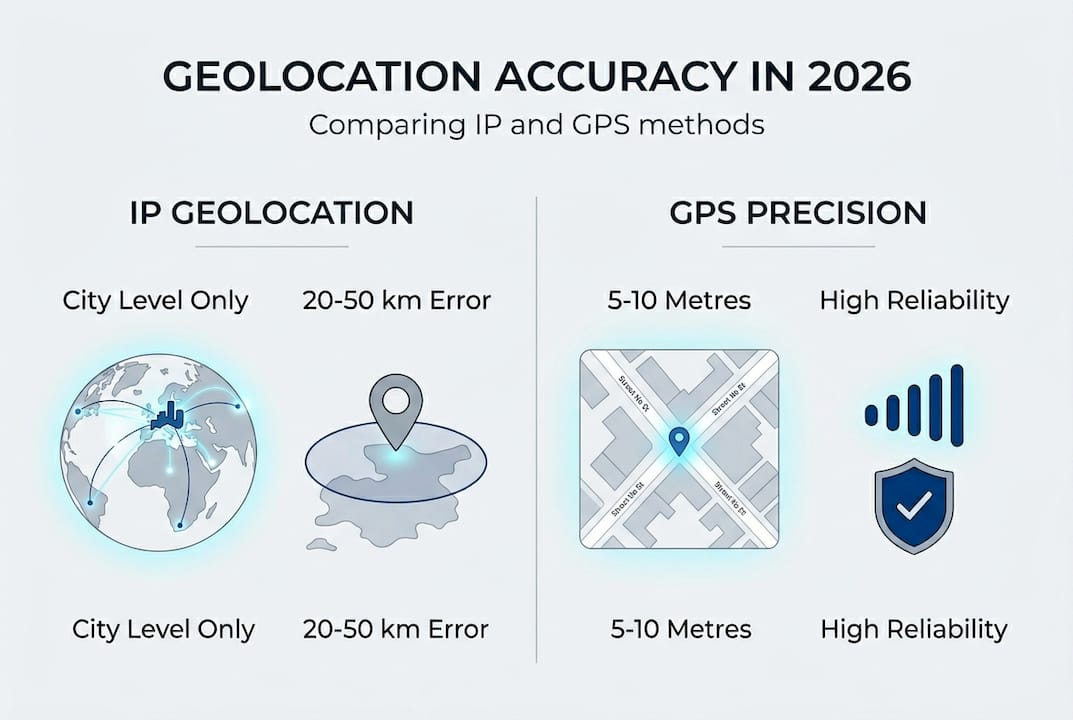
| IP versus GPS precision | GPS achieves metre-level accuracy whilst IP-based methods typically range from city-level precision with 20-50 km error margins |
| Major accuracy challenges | VPNs, proxies, dynamic IP reassignment, and outdated databases significantly compromise geolocation reliability in security contexts |
| Security applications | Accurate geolocation supports threat detection, fraud prevention, access control, and regulatory compliance for IT specialists |
What is geolocation accuracy?
Geolocation accuracy refers to the precision level achieved when determining a device’s or IP address’s geographic location through digital methods. For network security professionals managing IP addresses, understanding this concept means recognising that geolocation accuracy depends on data source quality, database completeness, and the technology employed. Accuracy is typically measured as an error margin expressed in kilometres or miles, representing the radius within which the actual location likely falls.
Several technical factors influence geolocation accuracy significantly. The quality of IP registration databases directly affects precision, as these repositories contain mapping information between IP address blocks and geographic regions. Static IP addresses generally provide more consistent geolocation data than dynamic addresses, which Internet Service Providers frequently reassign across different geographic areas. Mobile IP addresses present particular challenges, as devices move between cell towers and networks, causing location data to shift unpredictably.
Common accuracy metrics help security professionals gauge reliability. Country-level geolocation typically achieves 95-99% accuracy, making it reliable for broad geographic restrictions. City-level precision drops to 55-80% accuracy with error margins between 20-50 kilometres, whilst neighbourhood or street-level attempts rarely exceed 30% accuracy for IP-based methods. These ranges vary considerably based on the IP type, with corporate static IPs offering better precision than residential dynamic addresses or mobile connections.
The variability in accuracy based on IP characteristics requires careful interpretation. Corporate networks with registered static IP blocks provide relatively stable geolocation data, useful for baseline security policies. Residential users on dynamic IP assignments may appear to relocate frequently as ISPs rotate addresses within regional pools. Mobile networks introduce the greatest uncertainty, as IP geolocation explained methodologies struggle with rapid geographic movement and carrier-grade NAT implementations that mask individual device locations.
Pro Tip: Validate geolocation data by cross-referencing multiple IP intelligence sources and combining location signals with other contextual factors like timezone consistency, connection patterns, and historical access behaviour to improve confidence in security decisions.
Comparing IP-based and GPS geolocation accuracy
IP-based and GPS geolocation methods serve different purposes with dramatically different accuracy profiles. IP geolocation is generally less accurate than GPS but offers practical advantages for network security applications where device cooperation isn’t required. Understanding these differences helps you select appropriate methods for specific security scenarios and set realistic expectations for location-based access controls.
IP geolocation accuracy typically ranges from country-level certainty to city-level approximation, with error margins commonly between 20-50 kilometres in urban areas and potentially exceeding 100 kilometres in rural regions. This method relies on mapping IP address blocks to registered locations in databases maintained by Regional Internet Registries, ISPs, and commercial geolocation providers. The technique works passively, requiring no special permissions or device capabilities, making it ideal for analysing connection attempts, log files, and network traffic at scale.
GPS delivers metre-level precision, often within 5-10 metres under optimal conditions, by triangulating signals from multiple satellites. However, GPS requires active device cooperation, explicit user permissions, and hardware capabilities that IP-based methods bypass entirely. For security applications, GPS data proves valuable when available through mobile applications or endpoint security agents, but remains impractical for analysing arbitrary network connections or investigating historical security incidents where only IP addresses exist in logs.

| Method | Typical accuracy | Advantages | Limitations |
| — | — | — |
| IP geolocation | 20-50 km (city-level) | Passive, scalable, no device cooperation required | Affected by VPNs, proxies, dynamic IPs |
| GPS | 5-10 metres | High precision, real-time tracking | Requires device cooperation, permissions, hardware |
| Hybrid approach | Varies by context | Best of both methods, cross-validation | Complex implementation, higher resource cost |
Advantages of IP-based methods for mass security use include non-intrusive operation, scalability across millions of connections, and compatibility with existing log analysis workflows. Security teams can apply IP geolocation accuracy analysis to every authentication attempt, API request, or network connection without requiring client-side changes. This passive nature makes IP geolocation indispensable for threat intelligence, fraud detection, and compliance monitoring where you analyse traffic from unknown or untrusted sources.
Limitations significantly impact IP accuracy in security contexts. VPN usage masks true geographic location entirely, routing traffic through exit nodes potentially thousands of kilometres from the actual user. Proxy servers, Tor networks, and anonymisation services similarly obscure real locations. Dynamic IP address assignment by ISPs means the same user may appear in different cities across sessions as addresses rotate through regional pools. Mobile carrier-grade NAT implementations aggregate thousands of users behind single IP addresses, making individual geolocation impossible.
Pro Tip: Combine IP and GPS data where possible for security decisions, using IP geolocation as a first-pass filter for impossible travel scenarios and GPS for high-risk transactions requiring precise location verification, whilst always maintaining fallback authentication methods that don’t rely solely on location.
Challenges and limitations of geolocation accuracy in network security
Network security professionals face numerous obstacles when relying on geolocation accuracy for threat detection and access control. Understanding these challenges helps you develop realistic security policies that account for inherent limitations whilst still leveraging location data effectively. The most significant barriers arise from deliberate obfuscation technologies, infrastructure complexity, and data quality issues that compromise location reliability.
Major technical challenges include:
- VPN and proxy usage masks true geographic locations by routing traffic through intermediary servers, making use of VPNs, proxies, dynamic IP addresses compromises geolocation accuracy and complicating security assessments significantly
- Network Address Translation aggregates multiple users behind single public IP addresses, particularly in corporate environments and mobile networks, eliminating individual location granularity
- Dynamic IP address reassignment by ISPs causes the same address to represent different geographic locations over time, creating false positive alerts for impossible travel scenarios
- Database inaccuracies and staleness occur when IP block assignments change ownership or geographic registration without corresponding updates to commercial geolocation databases
- Mobile network complexity introduces uncertainty as devices roam between towers, switch carriers, and connect through distributed infrastructure that obscures precise location
- Cloud service adoption means applications and users increasingly connect through geographically distributed data centres rather than from actual user locations
The impact of these limitations on security risk assessments creates both false positives and false negatives. False positives occur when legitimate users appear suspicious due to VPN usage, corporate proxy routing, or ISP address pool reassignments, generating alert fatigue and wasting analyst time. False negatives arise when attackers deliberately operate from expected geographic regions, use residential proxy networks to appear legitimate, or compromise accounts from the victim’s actual location, evading location-based detection entirely.
Best practices to mitigate these risks include combining multiple detection methods rather than relying solely on geolocation. Correlate location data with behavioural analytics, device fingerprinting, and authentication patterns to build comprehensive risk profiles. Maintain continuously updated geolocation databases from reputable providers who actively verify IP block assignments. Implement tiered response strategies where location anomalies trigger additional authentication steps rather than automatic blocking, reducing false positive impact whilst maintaining security.
“Geolocation data should inform security decisions, not dictate them. The wisest security teams treat location as one signal among many, understanding that both attackers and legitimate users have reasons to obscure their true geographic position. Context and correlation matter more than any single data point.”
Expert security practitioners recognise that GPS accuracy factors guide principles apply broadly to all location technologies, emphasising the need for vigilance in interpreting geolocation data. Environmental factors, technical limitations, and deliberate obfuscation all introduce uncertainty that security policies must accommodate through defence in depth approaches rather than over-reliance on location alone.
Practical applications of geolocation accuracy for IT and security specialists
Geolocation accuracy delivers tangible value across multiple security functions when applied appropriately with awareness of its limitations. IT and security specialists leverage location data to detect anomalies, prevent fraud, enforce access policies, and meet regulatory requirements. Understanding these practical applications helps you integrate geolocation intelligence effectively into existing security workflows and incident response procedures.
Key use cases demonstrate geolocation’s security value:
- Detecting suspicious login attempts by identifying impossible travel scenarios where the same account authenticates from geographically distant locations within implausibly short timeframes
- Fraud prevention in financial services and e-commerce by flagging transactions originating from high-risk countries or locations inconsistent with customer profiles and purchase history
- Network access control through geographic restrictions that limit administrative interfaces, sensitive applications, or data repositories to specific countries or regions based on business requirements
- Threat intelligence enrichment by correlating attack sources with known malicious infrastructure, command and control servers, or regions associated with specific threat actor groups
- Incident response prioritisation by using location data to assess attack sophistication, potential attribution, and alignment with known threat campaigns targeting your organisation
Accurate geolocation supports threat detection, fraud prevention, and compliance requirements, particularly for organisations operating under regulations like GDPR that mandate data residency controls and cross-border transfer restrictions. Security teams use geolocation to verify that data access occurs from approved jurisdictions, audit cross-border data flows, and demonstrate compliance with geographic data sovereignty requirements to regulators and auditors.
Integrating geolocation data into incident response workflows requires systematic approaches. Configure SIEM platforms to enrich security events with geolocation context automatically, enabling analysts to spot geographic anomalies during alert triage. Establish baseline location profiles for users and systems, triggering elevated alerting when deviations occur. Implement graduated response procedures where location anomalies prompt additional verification steps, such as multi-factor authentication challenges or security questionnaires, rather than automatic blocking that might impact legitimate users.
| Security function | Geolocation reliance | Typical accuracy requirement | Key considerations |
|---|---|---|---|
| Fraud detection | High | City-level (20-50 km) | Balance false positives with risk tolerance |
| Access control | Medium | Country-level (95%+) | Account for VPN use by legitimate users |
| Threat intelligence | Medium | Country/region-level | Focus on patterns rather than individual events |
| Compliance auditing | High | Country-level (95%+) | Maintain detailed logs for regulatory review |
Best practice tips for IT professionals using geolocation data in daily security operations include maintaining multiple geolocation data sources to cross-validate suspicious events and reduce false positives. Utilise IP address lookup tool capabilities to investigate alerts quickly, combining location data with other IP intelligence like hosting provider, proxy detection, and threat reputation scores. Regularly review and update geographic access policies to reflect legitimate business travel, remote work arrangements, and organisational changes that affect expected user locations.
Implement contextual alerting that considers time of day, historical patterns, and user roles when evaluating location anomalies. A developer accessing systems from a new country during normal working hours presents different risk than an administrative account authenticating from an unexpected location at 3 AM. Leverage IP to location finder tools to build location baselines and identify gradual shifts in access patterns that might indicate account compromise or insider threats.
Document geolocation-based security decisions thoroughly, maintaining audit trails that demonstrate how location data influenced risk assessments and response actions. This documentation proves invaluable during incident investigations, compliance audits, and post-mortem analyses. Train security analysts to interpret geolocation data critically, understanding accuracy limitations and recognising scenarios where location signals may mislead rather than inform. The IP role in IT security extends beyond simple location lookup to comprehensive threat context that requires skilled interpretation.
Explore instant IP lookup tools for geolocation accuracy
To help you apply what you’ve learned, here are reliable tools that can enhance your geolocation accuracy and network security efforts. Instant IP Lookup provides a comprehensive suite of IP intelligence and geolocation tools specifically designed for security professionals who need rapid, accurate analysis of network connections and potential threats. These tools integrate seamlessly into security workflows, offering real-time insights that support informed decision-making during incident response and threat investigations.
Instant IP Lookup offers precise IP address lookup tool capabilities suited for security needs, delivering detailed geolocation data alongside ISP information, proxy detection, and threat intelligence in a single query. Security teams can quickly analyse IP accuracy for suspicious activity detection, correlating location data with other signals to build comprehensive threat profiles. The platform’s IP to location finder provides city-level precision where data quality permits, whilst clearly indicating confidence levels and potential accuracy limitations for each query.
Pro Tip: Use multiple Instant IP Lookup tools to cross-check and validate geolocation data for better security decisions, combining basic IP geolocation explained lookups with proxy detection and threat intelligence features to develop complete context around suspicious connections before taking enforcement actions.
Frequently asked questions
What is geolocation accuracy in the context of IP addresses?
Geolocation accuracy for IP addresses measures how precisely the physical location of an internet connection can be determined from its IP address alone. Typical accuracy ranges from highly reliable country-level identification to approximate city-level positioning with 20-50 kilometre error margins. The precision depends on database quality, IP type, and whether users employ privacy tools like VPNs. For detailed IP geolocation accuracy details, consider that static corporate IPs generally provide better accuracy than dynamic residential or mobile addresses.
How can network security professionals improve geolocation accuracy?
Security professionals improve geolocation accuracy by using multiple commercial geolocation databases and cross-referencing results to identify discrepancies. Regularly updating IP intelligence feeds ensures you work with current address block assignments rather than stale data. Combining geolocation with complementary signals like timezone consistency, connection patterns, and device fingerprinting creates more reliable security decisions than location data alone. Implementing hybrid approaches that validate IP geolocation against GPS data when available through endpoint agents further enhances accuracy for high-risk scenarios.
What are common causes of poor geolocation accuracy?
Poor geolocation accuracy primarily results from anonymisation technologies like VPNs and proxy servers that deliberately mask true user locations by routing traffic through intermediary servers. Frequent IP address reassignments by Internet Service Providers cause the same address to represent different locations over time, creating false positives in security monitoring. Outdated geolocation databases that haven’t incorporated recent IP block transfers or registration changes introduce systematic errors. Mobile networks with carrier-grade NAT and distributed infrastructure obscure individual device locations, whilst cloud services route connections through geographically dispersed data centres rather than actual user locations.
How can geolocation accuracy help detect suspicious network activity?
Geolocation accuracy enables detection of suspicious network activity by identifying impossible travel scenarios where accounts authenticate from distant locations within unrealistic timeframes. Geographic discrepancies between expected user locations and actual connection sources can indicate VPN or proxy use, potentially signalling account compromise or unauthorised access attempts. Security teams use detect suspicious activity with geolocation techniques to flag connections from high-risk countries, known malicious infrastructure, or regions inconsistent with user profiles and business operations. Geolocation supports contextual decision-making in alert triage, helping analysts prioritise investigations based on location risk factors whilst accounting for legitimate scenarios like business travel or remote work arrangements.

Comments (0)