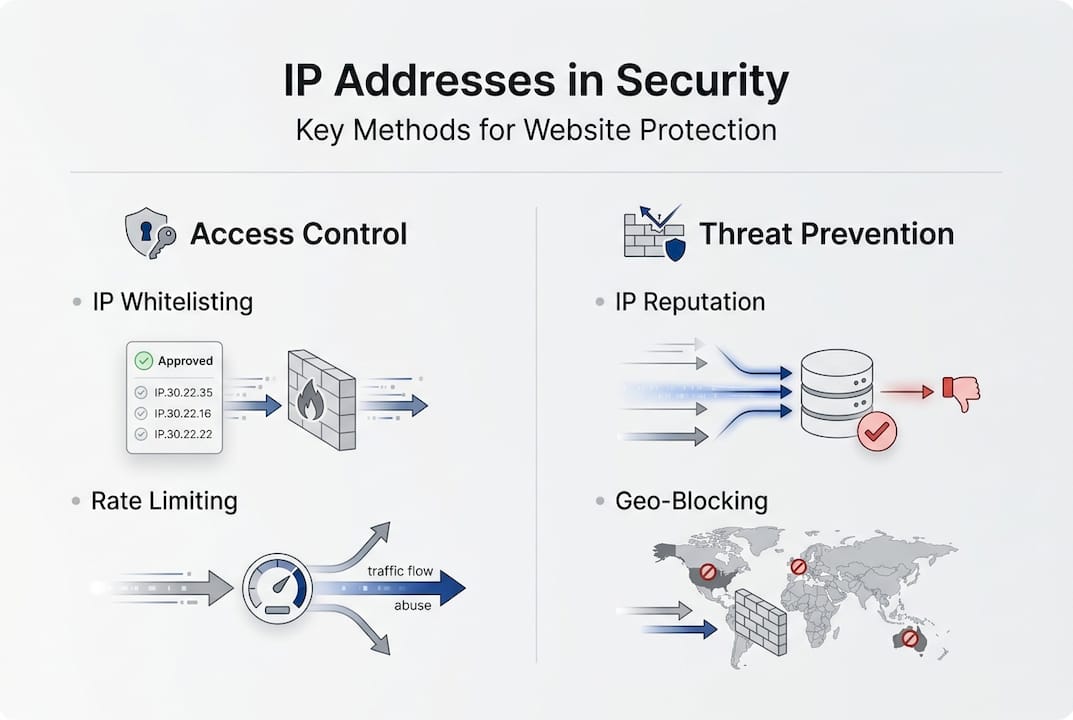
Many organisations assume that blocking or allowing specific IP addresses alone will secure their websites. This oversimplification ignores the nuanced reality: IP addresses serve as primary identifiers for access control, but they function best as one layer within a comprehensive defence strategy. IP-based controls excel at access management, rate limiting, and geo-blocking, yet they face significant limitations from IP spoofing, NAT sharing, and IPv6 adoption. Effective website security requires layering IP intelligence with identity verification and behavioural analysis to address modern threat landscapes.
Table of Contents
- Key takeaways
- IP addresses as foundational tools for website access control and rate limiting
- Leveraging IP reputation and geo-blocking for enhanced security
- Challenges and limitations of IP-based controls in modern network environments
- Building a robust website security strategy beyond IP address controls
- Enhance your IP-based website security with Instant IP Lookup tools
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| IP as foundation | IP addresses form the backbone of access control and rate limiting, but they work best as one layer in a broader defence strategy. |
| Layered defence approach | Effective website security requires layering IP controls with identity verification and behavioural analysis. |
| ASN reputation improves security | ASN reputation extends protection by covering whole networks under common control, making blocking more efficient than IP level alone. |
| IP spoofing and IPv6 complexities | IP spoofing, NAT sharing and IPv6 adoption create complexities that favour layered controls and careful rule management. |
IP addresses as foundational tools for website access control and rate limiting
IP addresses form the backbone of access control mechanisms across web infrastructure. Whitelisting restricts access to approved IPs, whilst blacklisting blocks known malicious sources. Dynamic denylisting takes this further by automatically adding IPs that exhibit suspicious behaviour, allowing security teams to respond to emerging threats in real time. NGINX Plus offers API-managed denylisting that updates IP restrictions without service restarts, providing operational flexibility for high-traffic environments.
CIDR notation enables scalable IP range management, allowing administrators to whitelist or blacklist entire network blocks rather than individual addresses. For instance, specifying 192.168.1.0/24 covers 256 addresses in a single rule, dramatically reducing configuration overhead. Modern implementations integrate IP controls with identity providers, requiring both approved IP origin and valid authentication credentials before granting access. This dual-factor approach mitigates risks from credential theft or IP spoofing attacks individually.
Rate limiting using IP addresses prevents abuse by tracking request volumes per IP over defined time windows. Cloudflare’s WAF allows rules like 100 requests per 10 seconds per IP, automatically throttling or blocking sources exceeding thresholds. Azure’s rate limiting similarly protects APIs from DDoS attacks and credential stuffing campaigns by identifying abnormal request patterns. AWS WAF integrates IP-based rate rules with managed threat intelligence feeds, blocking traffic from known bot networks before they reach application servers.
Rate limiting proves particularly effective against distributed attacks where individual IPs each send modest request volumes. By aggregating metrics across IP ranges or ASNs, security teams detect coordinated campaigns that single-IP analysis would miss. Cloudflare reports that rate limiting mitigates 70% of application-layer DDoS attempts when properly configured with graduated response actions from challenges to outright blocks.
Pro Tip: Combine IP whitelisting with multi-factor authentication for administrative interfaces. Even trusted IP ranges can be compromised through VPN credential theft or network pivoting, so identity verification adds critical defence depth.
For enhanced visibility into your own IP-based security posture, understanding the role of IP in IT support security troubleshooting helps diagnose access control issues and optimise rate limiting rules.
Leveraging IP reputation and geo-blocking for enhanced security
IP reputation systems aggregate threat intelligence from multiple sources to score addresses based on historical malicious activity. Unlike simple blacklists that flag individual IPs after abuse, reputation services provide predictive risk scoring before attacks occur. ASN reputation extends this concept to entire autonomous systems, recognising that malicious infrastructure often clusters within specific hosting providers or networks.
ASN reputation outperforms single IP blacklisting by covering thousands of addresses under common administrative control. Research indicates that 70% of online fraud originates from malicious ASNs, making ASN-level blocking far more efficient than reactive IP-by-IP responses. AWS WAF provides managed IP sets for known malicious sources, automatically updated as threat landscapes evolve, whilst allowing custom IP sets for organisation-specific requirements.
Geo-blocking uses IP geolocation to restrict access based on geographic origin. Organisations operating solely within specific regions can block entire countries, eliminating vast swathes of potential attack traffic. Gaming and financial services industries extensively deploy geo-blocking to comply with regulatory restrictions and reduce fraud exposure. However, geo-blocking affects SEO and user experience when legitimate users travel or access content via VPNs, requiring careful policy design.

| Approach | Scope | Reactivity | Effectiveness |
|---|---|---|---|
| IP blacklisting | Individual addresses | Reactive after abuse | Limited; attackers rotate IPs |
| ASN reputation | Entire networks | Proactive risk scoring | High; covers infrastructure clusters |
| Geo-blocking | Country/region | Policy-based | Moderate; VPNs bypass easily |
| Dynamic denylisting | Behavioural triggers | Real-time response | High for emerging threats |
IP reputation feeds require continuous updates to maintain effectiveness. Threat actors constantly acquire new infrastructure, rendering static blacklists obsolete within days. Subscription services from providers like Spamhaus, Proofpoint, and Cisco Talos offer hourly or real-time updates, ensuring protection against the latest campaigns. Integration with SIEM platforms enables automated response workflows that block high-risk IPs across firewalls, WAFs, and application layers simultaneously.
Pro Tip: Use dynamically updated IP sets rather than hardcoded blacklists. Threat infrastructure changes rapidly, and manual list maintenance introduces dangerous gaps in coverage.
To implement geo-blocking effectively, learn how to detect suspicious activity using geolocation IP trackers and understand what geo-blocking is and how it affects online access.
Challenges and limitations of IP-based controls in modern network environments
IP spoofing bypasses naive IP-based filters by forging source addresses in packet headers. Whilst TCP connections require bidirectional communication that complicates spoofing, UDP-based attacks and reflection amplification techniques exploit spoofed IPs to obscure attacker origins. Implementing unicast Reverse Path Forwarding (uRPF) at network edges validates that incoming packets arrive on interfaces consistent with routing tables, dropping spoofed traffic before it reaches application layers.
Network Address Translation (NAT) and Carrier-Grade NAT (CGNAT) share single public IPs among hundreds or thousands of users, making IP-based attribution nearly impossible. Blocking a malicious user behind CGNAT inevitably impacts innocent users sharing the same address. Mobile networks extensively use CGNAT, meaning IP-based controls can inadvertently block entire cellular subscriber bases. This limitation severely undermines IP whitelisting for user authentication, as dynamic IPs and shared NAT reduce whitelist effectiveness.
IPv6 adoption introduces new security considerations. The vast address space (2^128 addresses) makes IP-based scanning and blacklisting impractical, whilst the lack of NAT by default exposes all internal devices with globally routable addresses. Traditional perimeter security models assuming NAT-based hiding fail in IPv6 environments, requiring explicit firewall rules for every host. Many organisations delay IPv6 deployment due to these complexities, but CGNAT and IPv6 transition require careful planning to avoid security gaps.
- Dynamic IP allocation: ISPs frequently reassign addresses, making whitelists obsolete and blacklists ineffective as malicious IPs return to legitimate users
- Shared hosting environments: Cloud platforms and hosting providers assign multiple customers to single IPs, preventing granular access control
- VPN and proxy services: Legitimate users and attackers alike obscure true origins, rendering IP-based geo-blocking and reputation checks unreliable
- IPv6 privacy extensions: Temporary addresses change frequently to protect user privacy, complicating tracking and access control policies
- Lack of identity verification: IP addresses identify network endpoints, not users, allowing credential theft to bypass IP-based restrictions entirely
Bogon filtering blocks traffic from unallocated, reserved, or private IP ranges appearing on public interfaces, preventing spoofing attacks using these addresses. Regular updates to bogon lists are essential as IANA allocates previously reserved space to regional registries. Monitoring IPv6 deployment across your infrastructure ensures security policies adapt to dual-stack environments rather than leaving IPv6 traffic unfiltered.
Pro Tip: Deploy uRPF strict mode on edge routers and maintain updated bogon filters. Monitor IPv6 adoption carefully, ensuring firewall rules cover both protocols comprehensively.
Regular monitoring helps identify when your own IPs appear on blacklists, which can impact email delivery and reputation. Understand why you should regularly use an online blacklist checker tool and review IPv4 vs IPv6 differences for users to prepare for protocol transitions.
Building a robust website security strategy beyond IP address controls
IP-based controls are foundational but insufficient alone. Modern security frameworks layer IP intelligence with identity verification, behavioural analytics, and machine learning to create defence-in-depth strategies. Identity providers like Okta, Azure AD, and Auth0 authenticate users independently of network location, ensuring that compromised IP whitelists do not grant unauthorised access. Combining IP restrictions with multi-factor authentication requires attackers to compromise both network position and user credentials, dramatically increasing attack complexity.
Behavioural analysis examines user actions beyond simple IP metrics. Machine learning models detect anomalies like unusual access times, rapid geographic shifts, or atypical data access patterns that indicate compromised accounts. These models incorporate IP reputation as one feature among dozens, including device fingerprints, session duration, and API call sequences. When suspicious behaviour emerges, systems can require step-up authentication or temporarily restrict access regardless of IP whitelist status.
Machine learning enhances threat detection by identifying subtle patterns across massive datasets. Models trained on historical attack data recognise emerging campaigns before signature-based systems react. IP addresses contribute valuable context, such as ASN reputation, geolocation consistency, and connection frequency, which algorithms weight alongside application-layer signals. This holistic approach catches sophisticated attacks that evade single-layer defences.
- Multi-factor authentication (MFA): Requires possession factors beyond IP-based network access, protecting against credential theft
- Zero Trust architecture: Assumes breach and verifies every access request regardless of network origin or IP reputation
- Behavioural analytics: Detects anomalies in user actions that IP-based rules cannot identify
- Device fingerprinting: Tracks hardware and software characteristics to identify returning devices across IP changes
- Threat intelligence integration: Combines IP reputation with indicators of compromise from multiple sources for comprehensive risk assessment
- Adaptive authentication: Adjusts security requirements based on risk scores incorporating IP, behaviour, and context
| Approach | Pros | Cons |
|---|---|---|
| IP-only controls | Simple to implement, low computational overhead, effective for known threats | Easily bypassed via VPNs, ineffective against NAT/CGNAT, no identity verification |
| Layered security | Defence-in-depth resilience, adapts to sophisticated attacks, verifies identity and behaviour | Higher complexity, increased latency, requires ongoing tuning and monitoring |
Best practices integrate IP filtering at network perimeters to block obvious threats, identity providers for user authentication, and behavioural monitoring to detect compromised accounts. This layered approach ensures that failures in any single control do not compromise overall security. Regular policy reviews adapt rules to evolving threat landscapes, whilst automated response workflows reduce mean time to containment when incidents occur.
For foundational knowledge supporting these strategies, explore IP geolocation explained to understand how location data enriches security context.
Enhance your IP-based website security with Instant IP Lookup tools
Now that you understand the critical role IP addresses play within layered security strategies, practical tools help implement these defences effectively. Instant IP Lookup provides real-time IP address lookup and geolocation services that identify suspicious traffic sources, verify IP reputation, and detect proxy or VPN use. Our IP address lookup and geolocation tool delivers instant visibility into ISP details, geographic location, and network characteristics for any address.
Security teams use our platform to investigate suspicious IPs flagged by rate limiting rules or access logs, quickly determining whether sources originate from known malicious ASNs or unexpected geographic regions. The online blacklist checker tool verifies whether your own IPs appear on public blacklists, helping maintain email deliverability and reputation. Integrating these capabilities within your security workflows enhances IP-based controls with actionable intelligence, supporting the comprehensive defence strategies outlined throughout this article. For deeper understanding of the geolocation data powering these tools, review our guide on understanding IP geolocation.
Frequently asked questions
What is the main purpose of IP whitelisting in website security?
IP whitelisting restricts access exclusively to pre-approved IP addresses or ranges, creating a controlled perimeter around sensitive resources. This approach proves most effective for administrative interfaces, internal applications, and APIs requiring strict access control. However, whitelisting alone cannot verify user identity, making it vulnerable to credential theft or compromised trusted networks.
How does rate limiting by IP address prevent DDoS attacks?
Rate limiting tracks request volumes from each IP over defined time windows, automatically throttling or blocking sources exceeding thresholds. This prevents individual IPs or coordinated botnets from overwhelming servers with excessive requests. Advanced implementations aggregate metrics across IP ranges and ASNs to detect distributed attacks where each participating IP sends modest traffic individually.
Why is ASN reputation more effective than IP blacklisting?
ASN reputation addresses entire networks under common administrative control, covering thousands of addresses within malicious hosting providers or compromised infrastructure. Since attackers frequently rotate IPs within controlled ASNs, blocking at the network level prevents evasion through simple IP changes. Research shows 70% of online fraud originates from malicious ASNs, making this approach far more efficient than reactive IP-by-IP blocking.
What challenges does IPv6 introduce for IP-based security controls?
IPv6’s vast address space (2^128 addresses) makes comprehensive IP scanning and blacklisting impractical, whilst the protocol’s lack of NAT by default exposes all devices with globally routable addresses. Privacy extensions generate temporary addresses that change frequently, complicating tracking and access control. Organisations must implement explicit firewall rules for every host rather than relying on NAT-based hiding, requiring significant policy updates during IPv6 adoption.
How can I check if my IP address is blacklisted?
Regularly querying public blacklist databases identifies whether your IPs appear on spam, malware, or abuse lists that can impact email delivery and reputation. Automated monitoring services check dozens of blacklists simultaneously, alerting you to new listings so you can investigate root causes and request removal. For detailed guidance, see how to check if your IP is blacklisted and implement proactive monitoring within your security workflows.
Recommended
- Role of IP in IT support: security & troubleshooting 2026
- Everything You Need To Know About IP Addresses And Why They Matter In 2025 – Instant Ip Lookup
- Detect Suspicious Activity via IP Geolocation | Instant IP Lookup
- The Ultimate Guide To Using IP Lookup For Cybersecurity And Privacy – Instant Ip Lookup
- Security Tips for Protecting Your WordPress Themes – Simplehouse.dk

Comments (0)