Accurate IP address identification has become essential for protecting networks and responding to security incidents. When suspicious traffic appears or a breach occurs, you need reliable methods to trace IP origins, verify ownership details, and assess reputation quickly. This guide walks you through proven IP lookup techniques using geolocation databases, WHOIS queries, ASN analysis, and reputation checks, helping you gather comprehensive intelligence for threat detection and network troubleshooting.
Table of Contents
- Key takeaways
- Understanding IP address lookup and its importance
- Preparing for effective IP address lookup: tools and prerequisites
- Executing IP address lookup: step-by-step guide
- Verifying results and common troubleshooting in IP lookup
- Discover powerful IP lookup tools for IT professionals
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Core lookup methods | Geolocation, WHOIS, ASN and reputation checks are the primary techniques used to identify IP origins, ownership and trustworthiness. |
| Reliability through tools | Using multiple tools and databases increases accuracy and resilience against gaps in any single data source. |
| Understand results | Interpreting lookup outputs correctly is essential to avoid misattribution and misconfigured security controls. |
| Data quality matters | The usefulness of IP lookups depends on the currency and precision of geolocation data, registration details and threat intelligence feeds. |
Understanding IP address lookup and its importance
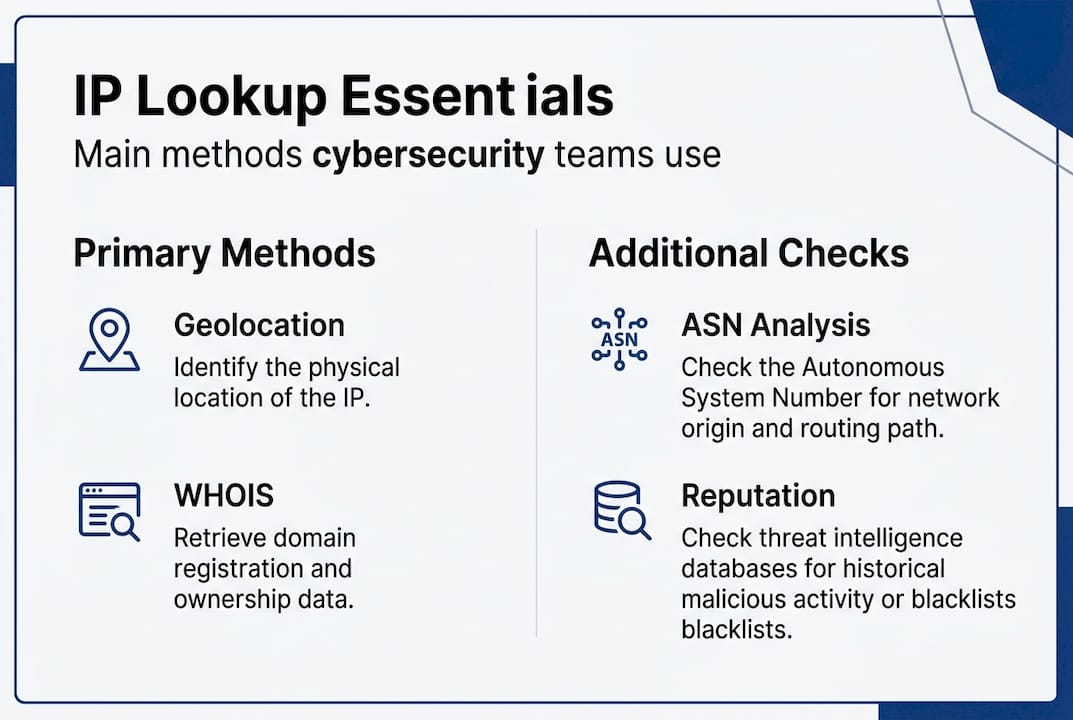
IP address lookup primarily involves geolocation databases, WHOIS queries, ASN analysis, and reputation checks for cybersecurity and network management. These methods transform raw IP addresses into actionable intelligence about geographic location, network ownership, routing infrastructure, and security reputation. Each approach reveals different facets of an IP’s identity and behaviour.
Geolocation services map IP addresses to physical locations by correlating network assignments with geographic boundaries. WHOIS databases store registration details including organisation names, contact information, and allocation dates. ASN lookups identify the autonomous system managing the IP block, revealing the network operator and routing relationships. Reputation checks query blacklists and threat intelligence feeds to flag IPs associated with malicious activity.
For cybersecurity operations, IP lookup serves multiple critical functions. You can detect suspicious activity via geolocation by identifying login attempts from unexpected countries or regions. Access control policies rely on IP reputation data to block known threat sources automatically. Incident response teams use domain WHOIS checker tools to trace attack infrastructure and identify responsible parties for takedown requests.
Network management benefits equally from comprehensive IP intelligence. Troubleshooting connectivity issues often requires identifying the upstream provider through ASN data. Capacity planning depends on understanding traffic sources by geographic distribution. Performance optimisation uses geolocation to route users to nearby servers.
Different lookup methods return distinct data types:
- Geolocation provides country, region, city, coordinates, and timezone estimates
- WHOIS reveals registrant organisation, registration dates, and administrative contacts
- ASN lookup shows autonomous system number, network operator name, and IP block assignments
- Reputation checks indicate blacklist status, spam history, and threat intelligence ratings
Combining these approaches creates a complete picture of any IP address, enabling informed decisions about security policies and network configurations.

Preparing for effective IP address lookup: tools and prerequisites
Successful IP lookup requires selecting appropriate tools and maintaining current data sources. The landscape includes specialised services for each lookup method, from simple web interfaces to API-driven automation platforms. Your choice depends on lookup volume, required detail level, and integration needs with existing security infrastructure.
Essential tool categories include:
- WHOIS query services providing registration and ownership details
- Geolocation databases mapping IPs to physical locations
- ASN lookup utilities identifying network operators and routing information
- Reputation checkers querying blacklists and threat intelligence feeds
- Integrated platforms combining multiple lookup methods in unified interfaces
| Tool Type | Primary Function | Typical Use Case | Update Frequency |
|---|---|---|---|
| Geolocation database | Maps IP to location | Access control, analytics | Monthly |
| WHOIS service | Reveals ownership | Incident response, compliance | Real-time |
| ASN lookup | Identifies network operator | Routing analysis, peering | Weekly |
| Reputation checker | Flags malicious IPs | Firewall rules, email filtering | Hourly |
Core methods of IP lookup require access to geolocation databases, WHOIS services, and reputation blacklists for comprehensive analysis. Free tools suffice for occasional queries, but high-volume operations benefit from commercial services offering better accuracy, fresher data, and API access for automation.
Data quality directly impacts lookup reliability. Geolocation databases vary in accuracy, with city-level precision ranging from 55% to 95% depending on the provider and region. WHOIS records may contain outdated contact details if registrants fail to update information. Reputation databases require continuous updates as threat actors constantly shift infrastructure.
Before executing lookups, verify you have:
- Access to multiple lookup services for cross-validation
- Current database versions from your chosen providers
- API credentials configured if automating queries
- Documentation of data retention and privacy policies
Pro Tip: Schedule monthly reviews of your lookup tool subscriptions to confirm database versions remain current, as outdated geolocation or reputation data can produce misleading results that compromise security decisions.
Integration with existing systems amplifies lookup value. Perform an IP lookup step by step by connecting lookup APIs to SIEM platforms for automatic enrichment of security events. Configure firewalls to query reputation services before allowing connections. Build custom dashboards displaying geographic traffic patterns from geolocation data.
Maintaining a toolkit of privacy and security tools ensures you can investigate IPs from multiple angles, adapting your approach based on the specific security or troubleshooting scenario you face.
Executing IP address lookup: step-by-step guide
Systematic IP lookup follows a structured process that gathers complementary data from multiple sources. Starting with basic identification and progressing to detailed analysis ensures you capture all relevant intelligence whilst avoiding premature conclusions based on incomplete information.
-
Begin with geolocation lookup to establish the IP’s apparent physical location, including country, region, city, and coordinates. Note the confidence level if provided, as accuracy varies significantly by location.
-
Query WHOIS databases to retrieve registration details, including the organisation holding the IP block, registration date, and administrative contacts. Record the Regional Internet Registry managing the allocation.
-
Perform ASN lookup to identify the autonomous system number and network operator. This reveals the actual service provider, which may differ from the organisation listed in WHOIS records.
-
Check reputation databases and blacklists to determine if the IP has known associations with malicious activity, spam, or compromised systems. Note any threat intelligence tags or risk scores.
-
Cross-reference results across sources to identify discrepancies and validate findings. Geographic location from geolocation should align with the organisation’s known presence. ASN operator should match expected providers for that region.
-
Document all findings with timestamps, as IP assignments and reputation status change over time. Historical context proves valuable when investigating patterns or tracking threat actors.
Using multiple lookup methods—including geolocation, WHOIS, ASN, and reputation checks—ensures accurate and thorough IP address analysis by revealing different aspects of the IP’s identity and behaviour that single-source queries miss.
Interpreting results requires understanding what each data point indicates. Geolocation shows where the IP appears to originate, but VPNs, proxies, and mobile networks can obscure true locations. WHOIS reveals the official registrant, though many organisations use privacy services or outdated contact details. ASN identifies the network operator, which is particularly useful for understanding routing paths and identifying hosting providers.
Reputation data requires careful interpretation. A single blacklist entry may represent a false positive, whilst presence on multiple lists strongly suggests malicious activity. Consider the blacklist’s focus: some target spam sources, others track malware distribution or scanning activity. Recent listings carry more weight than historical entries from years past.
Pro Tip: Automate repetitive lookups by scripting API calls to your chosen services, storing results in a database for trend analysis and historical comparison, which reveals patterns invisible in individual queries.
For practical implementation, perform an IP lookup step by step using web interfaces initially to understand result formats and data quality. Progress to API integration once you identify reliable sources and establish standard workflows. Combine automated lookups with manual investigation for high-priority security incidents requiring detailed analysis.
The domain WHOIS checker complements IP lookup when investigating web-based threats, revealing relationships between domain registrations and IP assignments that expose attacker infrastructure.
Verifying results and common troubleshooting in IP lookup
Accurate interpretation of IP lookup data and awareness of limitations such as inaccurate geolocation or outdated WHOIS records is essential for effective network management. Validation prevents costly mistakes from acting on incorrect intelligence, whilst troubleshooting skills help resolve discrepancies between conflicting sources.
Common issues affecting lookup reliability include:
- Inaccurate geolocation placing IPs in wrong cities or countries, particularly for mobile networks and satellite connections
- Proxy and VPN services masking true IP origins, showing data centre locations instead of actual user positions
- Outdated WHOIS records containing obsolete contact details or organisation names from previous assignments
- Regional Internet Registry delays causing newly allocated IP blocks to lack proper geolocation mapping
- Shared hosting environments where multiple organisations use the same IP address
Verification methods strengthen confidence in findings. Cross-reference geolocation results from multiple providers to identify outliers. Compare WHOIS registrant details against known information about the organisation. Validate ASN assignments through Regional Internet Registry databases. Check reputation across several blacklist services rather than relying on single sources.
| Error Type | Symptom | Corrective Action |
|---|---|---|
| Geolocation mismatch | Location contradicts known facts | Query multiple geolocation providers, consider proxy use |
| Stale WHOIS data | Contact details obviously outdated | Check RIR databases directly, note last update timestamp |
| Missing ASN info | No autonomous system found | Verify IP is publicly routable, check for recent allocation |
| False positive reputation | Blacklist entry seems incorrect | Investigate listing reason, check multiple reputation sources |
Troubleshooting geolocation discrepancies starts with recognising that accuracy varies by IP type. Fixed broadband connections typically geolocate to city level with reasonable accuracy. Mobile networks often show carrier infrastructure locations rather than device positions. Corporate networks using proxy servers appear at proxy locations, not employee sites.
WHOIS troubleshooting requires understanding registration hierarchies. Regional Internet Registries allocate large blocks to national registries or major ISPs, who subdivide and reallocate to customers. The WHOIS chain may require multiple queries to reach the actual user organisation. Privacy services intentionally obscure registrant details, showing proxy contact information instead.
Reputation false positives occur when legitimate IPs share space with malicious actors or inherit bad reputations from previous assignments. Investigate blacklist reasons through detailed lookup tools that show why an IP was listed. Recent listings deserve more scrutiny than old entries that may no longer apply.
Incorrect IP data undermines security decisions in multiple ways. Blocking legitimate traffic based on geolocation errors frustrates users and damages business operations. Allowing malicious connections due to outdated reputation data enables attacks. Misidentifying network operators during incident response wastes time and delays mitigation.
Validation becomes critical for high-stakes decisions. Before blocking entire IP ranges, verify reputation across multiple sources and investigate recent activity patterns. When tracing attacks, confirm WHOIS details through independent channels rather than assuming accuracy. Cross-check geolocation against other indicators like timezone in log timestamps or language preferences in HTTP headers.
Understanding IP lookup explained helps interpret results correctly and recognise when findings require additional investigation. The role of IP in security and troubleshooting demonstrates how accurate lookup data supports broader IT operations beyond individual queries.
Discover powerful IP lookup tools for IT professionals
Streamline your security workflows with comprehensive IP intelligence platforms designed for IT professionals. When you need instant access to geolocation data, WHOIS details, and reputation checks in one place, specialised tools eliminate the need to query multiple services separately.
The IP lookup and geolocation tool delivers detailed analysis including ISP identification, geographic coordinates, and timezone information in seconds. Combined with the step by step IP lookup guide, you can master efficient investigation techniques that save time during incident response. Understanding what you discover matters as much as the data itself, which is why IP lookup result explanations help you interpret findings correctly and avoid common misinterpretations that lead to poor security decisions.
Frequently asked questions
What is the difference between geolocation and WHOIS in IP lookup?
Geolocation maps an IP address to a physical location using databases that correlate network assignments with geographic boundaries, showing country, city, and coordinates. WHOIS queries reveal registration and ownership information including the organisation holding the IP block, administrative contacts, and allocation dates. Geolocation answers where an IP appears physically, whilst WHOIS answers who controls it legally.
How reliable are IP geolocation results for cybersecurity use?
Geolocation accuracy varies from 55% to 95% at city level depending on the provider, region, and connection type, making it useful for general threat assessment but insufficient as sole evidence. Fixed broadband connections geolocate more accurately than mobile networks or satellite connections. Complement geolocation with WHOIS records and reputation checks to build reliable intelligence, as VPNs and proxies can completely obscure true locations.
Can IP address lookup detect proxies and VPNs?
Yes, specialised proxy server detection tools identify many proxies and VPNs by checking IP addresses against known data centre ranges, analysing connection patterns, and querying reputation databases that track anonymisation services. However, detection is not foolproof as sophisticated VPNs using residential IP addresses or private proxy networks can evade identification. Combining multiple detection methods improves accuracy.
What are common mistakes when performing IP lookup?
Relying on a single data source without cross-validation leads to accepting inaccurate or incomplete information as fact. Ignoring timestamps and update frequencies results in basing decisions on outdated WHOIS records or stale reputation data. Misinterpreting geolocation as definitive proof of physical location overlooks VPNs, proxies, and mobile network complexities. Failing to document lookup results prevents historical analysis and pattern recognition across multiple incidents.

Comments (0)