TL;DR:
- Proxy detection requires adaptable, multi-layered methods to combat evolving tactics in 2026.
- Combining reputation, behavioral, analytical, and content analysis improves accuracy and reduces evasion.
- Ongoing process review and threat intelligence integration are critical for long-term effectiveness.
Separating genuine users from proxy-driven traffic has never been more demanding. Proxy tactics have grown sharply more sophisticated, with threat actors now routing connections through residential and mobile networks to blend in with legitimate users. Security teams that rely on outdated detection logic are increasingly exposed. Continuous adaptation is non-negotiable as proxies evolve beyond simple data-centre addresses into near-invisible residential and mobile endpoints. This article walks through the criteria that define effective proxy detection, the leading techniques available in 2026, a side-by-side comparison of approaches, and a practical framework for matching strategy to your specific network environment.
Table of Contents
- Establishing criteria for effective proxy detection
- Top proxy detection techniques in 2026
- Comparing detection options: strengths and weaknesses
- Selecting the right approach for your network
- Why constant adaptation matters more than any single proxy detection tool
- Strengthen your proxy detection strategy with Instant IP Lookup
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Adapt detection continuously | The most effective proxy detection evolves alongside new threats and proxy technologies. |
| Use multiple techniques | Combining detection methods delivers higher accuracy and better threat coverage. |
| Prioritise transparency | Choose solutions that offer clear reporting and explainable actions for easier troubleshooting. |
| Tailor to your network | Select proxy detection strategies that match your business’s size, risks, and resources. |
| No single tool suffices | Rely on a blend of tools, updates, and human insight to stay ahead of proxy threats. |
Establishing criteria for effective proxy detection
Before committing to any detection method, you need a clear set of criteria against which to measure it. Jumping straight to tooling without this framework is how teams end up with expensive solutions that still miss the traffic they care about most.
The five criteria that matter most are:
- Detection precision: How accurately does the system distinguish proxy traffic from legitimate users? High precision keeps false positives low and protects genuine customers from being blocked.
- Speed: Detection must happen at wire speed for high-traffic environments. A system that introduces latency defeats the purpose.
- Adaptability: Proxies evolve to residential and mobile endpoints constantly, so your detection logic must update in near real time.
- False positive and false negative rates: Both matter. False positives frustrate real users; false negatives let threats through.
- Scalability: A solution that works for 10,000 requests per day must also hold up at 10 million.
Integrating threat intelligence feeds is one of the most underrated ways to improve all five criteria simultaneously. Feeds that aggregate known proxy ranges, autonomous system numbers (ASNs), and flagged IP blocks give your detection engine fresh data without requiring manual research. Pairing this with a solid web traffic monitoring guide helps teams understand where anomalies originate and how to respond.
Transparency in reporting is often overlooked. When a detection system flags traffic, your team needs to understand why. Black-box decisions create operational blind spots and make tuning almost impossible.
Pro Tip: Prioritise solutions that offer explainable outputs, such as a confidence score alongside the reason for flagging. This makes threshold tuning far more precise and gives your team the evidence needed to act quickly.
Top proxy detection techniques in 2026
With clear criteria in place, the next step is understanding which detection methods are actually delivering results in 2026.
IP reputation checks remain the fastest first line of defence. Cross-referencing incoming IPs against curated databases of known data-centre ranges, Tor exit nodes, and flagged ASNs catches a significant volume of low-effort proxy use immediately. They work best for high-traffic web applications where speed is paramount. Understanding how to tell if an IP is a proxy starts here.
Active probing sends deliberate test packets to the connecting IP to check for inconsistencies in routing behaviour. It is more resource-intensive but surfaces proxies that reputation databases have not yet catalogued.
Connection analysis examines metadata such as round-trip time, TCP fingerprint, and header anomalies. Proxies often introduce measurable latency patterns or header inconsistencies that genuine connections do not produce.

Deep packet inspection (DPI) analyses the actual content and structure of packets. It is highly effective in sensitive environments such as financial services or government networks, though it carries significant processing overhead.
Behaviour analytics tracks how a session unfolds over time, mouse movement patterns, click cadence, and navigation paths. This is where machine-learning-enhanced proxy detection proves its value, adapting to hidden and rotating proxies that static rules would never catch.
The methods above are most powerful in combination. No single technique covers every evasion tactic. Using a layered proxy detection tool that combines reputation, behavioural, and analytical signals gives you the depth needed to address sophisticated threats, including those tied to fraud prevention with proxy detection.
Expert note: Machine learning is no longer optional for teams dealing with rotating or residential proxies. Rule-based systems alone cannot keep pace with the rate at which evasion techniques evolve. ML models trained on diverse traffic datasets consistently outperform static detection in precision and adaptability.
Comparing detection options: strengths and weaknesses
Once you understand the main methods, comparing them directly helps you allocate resources wisely. Detection tools must balance precision, adaptability, and processing demand, and no single approach wins on every dimension.
| Detection method | Accuracy | Evasion difficulty | False positive risk | Speed | Best scenario |
|---|---|---|---|---|---|
| IP reputation check | Moderate | Low | Low | Very fast | High-volume web apps |
| Active probing | High | Moderate | Low | Moderate | Unknown or novel IPs |
| Connection analysis | High | Moderate | Moderate | Fast | Mid-tier environments |
| Deep packet inspection | Very high | High | Low | Slow | Sensitive or regulated networks |
| Behaviour analytics | Very high | Very high | Moderate | Moderate | E-commerce, financial services |
Key observations from this comparison:
- IP reputation is your fastest filter but will not catch residential proxies that have clean histories.
- DPI offers the highest accuracy but demands significant compute resources, making it impractical for most high-volume environments without dedicated hardware.
- Behaviour analytics is the hardest to evade but requires sufficient session data to function well, meaning it is less effective on very short sessions.
- Connection analysis sits in a useful middle ground, offering solid accuracy without the overhead of DPI.
Using a detection tool guide alongside your comparison helps teams map these trade-offs to their actual infrastructure. For environments where suspicious patterns need rapid investigation, tools that identify suspicious connections in real time are invaluable.
Pro Tip: For critical systems such as payment gateways or authentication endpoints, consider a hybrid approach. Automate the first two or three detection layers, then route borderline cases to a human analyst for final review. This keeps throughput high while minimising costly errors.
Selecting the right approach for your network
With options compared, the practical question becomes: which blend fits your environment? Detection strategies should evolve as proxy tactics and network threats change, so treat this as an ongoing process rather than a one-time decision.
Follow these steps to match your detection approach to your business needs:
- Assess your risk profile. Define what a successful proxy bypass would cost you. Ad click fraud prevention has different stakes than protecting a government portal.
- Audit your current traffic volumes. Detection methods that work at 50,000 requests per day may not scale to 5 million.
- Identify your most sensitive endpoints. Apply your most resource-intensive methods, such as DPI or behaviour analytics, selectively to these areas rather than across all traffic.
- Integrate threat intelligence feeds. Automate updates to your IP reputation lists and proxy databases so your detection logic reflects current threat landscapes.
- Establish a review cadence. Schedule monthly or quarterly reviews of detection thresholds, false positive rates, and emerging proxy types.
The table below links common risk factors to recommended detection techniques:
| Risk factor | Recommended technique | Priority |
|---|---|---|
| High fraud exposure | Behaviour analytics plus IP reputation | Critical |
| Large anonymous user base | Connection analysis plus active probing | High |
| Regulated data environment | Deep packet inspection | Critical |
| Ad platform or affiliate network | IP reputation plus behaviour analytics | High |
| Small network with limited budget | IP reputation checks | Moderate |
For small networks, a well-maintained IP reputation check is often sufficient and cost-effective. Midsized organisations benefit from adding connection analysis to catch more sophisticated evasion. Enterprise environments should layer all five methods, with ML-driven behaviour analytics as the final arbiter. Investing in stronger online security at the infrastructure level compounds the value of every detection layer you add.
Why constant adaptation matters more than any single proxy detection tool
Here is an uncomfortable truth that the security industry rarely says plainly: the tool you deploy today will be partially obsolete within twelve months. Not because it is poorly built, but because the adversaries it is designed to catch are actively working to circumvent it.
Teams that invest heavily in a single detection platform and then treat it as a solved problem consistently fall behind. The proxy landscape shifts fast. Residential proxy networks now offer millions of rotating IPs sourced from real consumer devices, making them nearly indistinguishable from genuine traffic without behavioural context. Continuous adaptation to new proxy types is not a recommendation; it is the baseline expectation.
What actually separates high-performing security teams is not their tooling budget. It is their process. Teams that schedule regular reviews of detection criteria, actively monitor emerging proxy behaviours, and integrate new intelligence feeds outpace adversaries consistently. The human factor matters enormously here. Automated systems catch the patterns they are trained on. Analysts catch the anomalies that fall outside those patterns. VPN detection tool insights are a useful complement to proxy detection, particularly as the line between VPN and proxy use continues to blur in practice. Build adaptation into your process, not just your tooling.
Strengthen your proxy detection strategy with Instant IP Lookup
You can put this knowledge to work right now with the advanced resources available on InstantIPLookup.com.
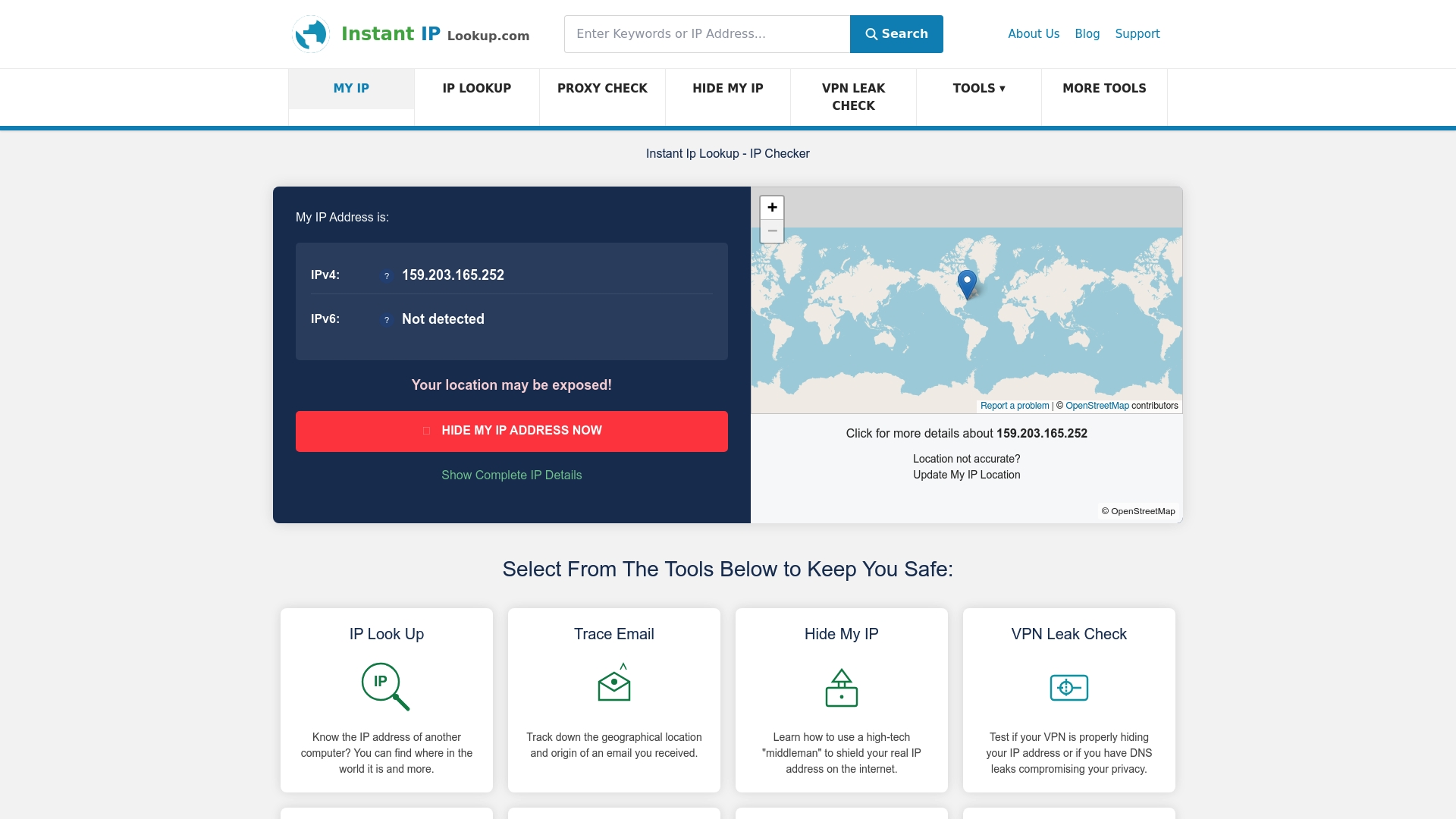
InstantIPLookup.com offers a full suite of proxy server detection tool capabilities alongside real-time IP address lookup services, giving your team immediate visibility into the traffic hitting your network. Whether you are investigating a suspicious connection, validating your detection thresholds, or building a broader security posture, the platform provides the diagnostic depth you need. Explore our IP lookup guide for step-by-step guidance on integrating these tools into your network management workflow and start making more informed decisions about the traffic you trust.
Frequently asked questions
What is the fastest way to identify a proxy user?
IP reputation and automated detection are the fastest methods, cross-referencing incoming IPs against known proxy databases in milliseconds. For speed-critical environments, this should always be your first filter.
Can residential proxies be detected easily in 2026?
Residential proxies are significantly harder to identify because they use real consumer IP addresses. Advanced behavioural and machine-learning techniques are required to reliably distinguish them from genuine traffic.
How does machine learning improve proxy detection?
Machine-learning-enhanced proxy detection uncovers new evasion patterns and adapts to rotating or hidden proxies that static rule sets would miss entirely. It is particularly effective when trained on diverse, high-volume traffic datasets.
What should I do if I get false positives?
Regularly review your detection thresholds, incorporate human oversight for borderline cases, and keep your threat intelligence feeds current. Explainable detection outputs make this tuning process considerably more efficient.
Is there a single tool that solves all proxy detection challenges?
No single solution keeps up without regular updating and adaptation. Multi-method strategies that layer reputation checks, behavioural analytics, and human review consistently outperform any standalone tool.

Comments (0)