Most cybersecurity professionals understand firewalls and encryption, yet many underestimate the risks lurking in exposed IP addresses. Your IP reveals far more than a network identifier. It discloses geolocation, ISP details, and organisational data that attackers exploit for reconnaissance, tracking, and targeted attacks. Despite common beliefs that basic anonymisation suffices, IP exposure remains a critical vulnerability enabling diverse cyberattacks. This guide explains why protecting IP information is vital for robust online security and privacy, detailing the risks, limitations of standard defences, and advanced strategies to safeguard your network infrastructure effectively.
Table of Contents
- Key takeaways
- Understanding the risks of exposed IP information
- Limitations of common IP anonymisation techniques
- Advanced IP protection strategies for network administrators
- Implications of IP exposure in modern cyber threats and compliance
- Protect your IP information with instant IP lookup tools
- Frequently asked questions about IP information protection
Key Takeaways
| Point | Details |
|---|---|
| IP exposure risks attacks | Exposed IP addresses enable targeted attacks and tracking by revealing geolocation, ISP and organisational information. |
| Revealed data fuels reconnaissance | Threat actors correlate IP data with other metadata to build detailed profiles of networks and user behaviour. |
| Weak anonymisation limits privacy | Common methods like truncation leave residual data and can still enable reidentification when paired with metadata. |
| IP data under GDPR | The GDPR classifies IP addresses as personal data when they can identify individuals directly or through other information, increasing compliance obligations. |
Understanding the risks of exposed IP information
Your IP address functions as a digital fingerprint. When exposed, it opens pathways for attackers to exploit your network. Exposed IP addresses enable attackers to launch targeted attacks including DDoS, IP spoofing, BGP hijacking, and port scanning for vulnerabilities. Each attack vector leverages the visibility of your IP to compromise availability, integrity, or confidentiality.
Beyond direct attacks, IP addresses reveal geolocation, ISP, and organisation info, facilitating reconnaissance, tracking, and deanonymisation attacks. Threat actors correlate this data with other metadata to build detailed profiles of your network topology and user behaviour. This intelligence gathering phase precedes sophisticated intrusions, making IP exposure a foundational vulnerability.
The risks multiply when IP data combines with other identifiers:
- Geolocation data narrows physical locations to city or neighbourhood levels
- ISP information reveals network infrastructure and potential security postures
- Organisational details expose business relationships and supply chain connections
- Temporal patterns enable tracking of user activity and movement
Pro Tip: Regularly audit your public-facing IP addresses using IP geolocation tools to understand what information adversaries can harvest about your network perimeter.
“IP exposure transforms anonymous network traffic into trackable digital footprints, enabling persistent surveillance and targeted exploitation across sessions and platforms.”
The convergence of these data points creates a comprehensive attack surface. Adversaries leverage exposed IPs to bypass perimeter defences, craft convincing social engineering attacks, and establish persistence within compromised networks. Understanding these IP address fraud threats is the first step toward implementing effective countermeasures.
Limitations of common IP anonymisation techniques
Many organisations rely on IP truncation or masking, believing these methods provide adequate privacy protection. This assumption creates dangerous security gaps. Common anonymisation like IP truncation fails: it provides inconsistent privacy, remains PII under GDPR when combined with metadata, and risks compliance violations. The technique typically removes the last octet of an IPv4 address, but this still leaves sufficient information for correlation attacks.
The GDPR specifically classifies IP addresses as personal data when they can identify individuals directly or through combination with other information. Truncated IPs paired with timestamps, user agents, or session cookies often enable reidentification. Regulatory bodies have issued fines for organisations that assumed truncation satisfied anonymisation requirements without conducting proper risk assessments.
Several critical weaknesses plague basic anonymisation approaches:
- Truncation preserves network topology information useful for reconnaissance
- Metadata correlation enables linking truncated IPs to specific users
- Geolocation databases still resolve truncated addresses to approximate locations
- Log aggregation across systems can reconstruct full IP addresses
- Dynamic IP reassignment creates false anonymity assumptions
The limitations extend beyond compliance concerns. Attackers exploit these weaknesses by collecting truncated IP logs from multiple sources and cross-referencing them with publicly available data. This process, known as dataset linkage, reconstructs user identities and behaviours with surprising accuracy. Even public Wi-Fi environments compound these risks through shared network segments.
Pro Tip: Conduct privacy impact assessments before implementing any IP anonymisation scheme, testing whether the method withstands correlation attacks using your actual data ecosystem.
Organisations must recognise that anonymisation is not a binary state but a spectrum. The effectiveness depends on the threat model, data retention policies, and broader security architecture. Relying solely on truncation without complementary controls like encryption, access restrictions, and monitoring creates a false sense of security. Understanding these IP anonymisation challenges guides the development of more robust protection strategies.
Advanced IP protection strategies for network administrators
Effective IP protection requires layered defences combining administrative controls, encryption, and architectural design. Start by implementing ingress/egress filtering, IP whitelisting, firewalls, VPNs, and management interface isolation to prevent exposure. These foundational controls establish network perimeter security and limit unnecessary IP visibility to external networks.
Management interface protection deserves particular attention. Isolate administrative access to dedicated VLANs or out-of-band networks, restricting connections to HTTPS only from authorised IP ranges. This separation prevents attackers from discovering management IPs through reconnaissance scans. Implement certificate-based authentication and multi-factor verification to add defence layers beyond IP-based access controls.

For advanced protection, prioritise cryptographic IP encryption (IPCrypt) over truncation for logging and sharing, and integrate with zero-trust frameworks and MTD address hopping in SDN for IoT environments. IPCrypt encrypts IP addresses in logs and analytics while preserving the ability to perform network operations, offering superior privacy without sacrificing functionality.
Implement these strategic controls systematically:
- Deploy stateful firewalls with default-deny policies for all IP traffic
- Configure ingress filtering to block spoofed source addresses at network edges
- Establish egress filtering to prevent unauthorised outbound connections
- Implement IP whitelisting for critical services and management interfaces
- Segment networks using VLANs to contain lateral movement
- Enable VPN tunnels for remote access, hiding internal IP addressing
- Deploy intrusion detection systems monitoring for IP-based reconnaissance
- Utilise dynamic address hopping in software-defined networks
Pro Tip: Combine static IP whitelisting with time-based access policies, automatically expiring administrative access windows to reduce exposure duration even if credentials are compromised.
The following table compares protection methods by effectiveness:
| Protection Method | Privacy Level | Operational Impact | Compliance Strength | Implementation Complexity |
|---|---|---|---|---|
| IP Truncation | Low | Minimal | Weak | Low |
| VPN Tunnelling | High | Moderate | Strong | Moderate |
| IPCrypt Encryption | Very High | Low | Very Strong | Moderate |
| Zero-Trust Architecture | Very High | High | Very Strong | High |
| Dynamic Address Hopping | High | Moderate | Strong | High |
These controls reduce your attack surface dramatically. Network segmentation limits blast radius when breaches occur, while encryption prevents IP disclosure even if logs are compromised. Monitoring systems detect anomalous patterns indicating reconnaissance or exploitation attempts. Understanding what IP lookup results reveal helps you assess which data points require the strongest protection.
Zero-trust frameworks enhance IP protection by eliminating implicit trust based on network location. Every connection request undergoes authentication and authorisation regardless of source IP, preventing lateral movement even if attackers compromise internal addresses. This approach particularly suits organisations with distributed workforces and cloud infrastructure where traditional perimeter models fail. Detailed guidance on securing administrative access provides implementation frameworks.
For cutting-edge protection, explore cryptographic IP encryption techniques that maintain operational utility whilst achieving strong privacy guarantees. These methods enable analytics and troubleshooting without exposing raw IP addresses, balancing security requirements with business needs.
Implications of IP exposure in modern cyber threats and compliance
The financial and operational impacts of IP exposure have escalated dramatically. Businesses lose $4.35M average per breach, with Verizon’s 2025 DBIR showing 60% of breaches involve human or IP-related factors and vulnerability exploits up 34%. These statistics underscore how IP exposure contributes directly to breach costs through enabling reconnaissance and initial access.

The healthcare sector faces particularly acute risks. The same research reveals that 66% of hospitals use pixels leaking IP and PHI, increasing breach risk substantially. Third-party tracking pixels embedded in patient portals and telehealth platforms transmit IP addresses alongside protected health information to advertising networks, creating HIPAA violations and privacy breaches. Regulators have begun enforcement actions against healthcare organisations for these disclosures.
Emerging attack vectors exploit IP exposure in sophisticated ways. NAT bypass via off-path TCP attacks infers private IPs, whilst IoT devices are exploited as proxies for credential stuffing and financial fraud. These techniques demonstrate that even RFC 1918 private addressing offers limited protection when attackers leverage protocol weaknesses and compromised endpoints.
The threat landscape includes diverse exploitation methods:
- Credential stuffing attacks routing through compromised IoT devices to obscure attacker IPs
- BGP hijacking redirecting traffic by exploiting exposed autonomous system numbers
- DDoS amplification attacks leveraging publicly visible reflector IPs
- Ransomware campaigns targeting organisations identified through IP reconnaissance
- Supply chain attacks mapping vendor relationships via IP address correlations
Compliance frameworks increasingly mandate IP protection as a core security control. GDPR, CCPA, and HIPAA all classify IP addresses as personal or protected data under specific contexts. Organisations must implement technical and administrative safeguards preventing unauthorised IP disclosure, maintain audit trails of IP data processing, and conduct regular assessments of anonymisation effectiveness. Understanding how personal data relates to IP scans clarifies regulatory obligations.
The following comparison illustrates varying threat severity:
| Threat Type | IP Exposure Role | Typical Impact | Mitigation Priority |
|---|---|---|---|
| DDoS Attacks | Direct targeting | Service disruption | Critical |
| Reconnaissance | Intelligence gathering | Breach precursor | High |
| Credential Stuffing | Proxy obfuscation | Account compromise | High |
| BGP Hijacking | Route manipulation | Traffic interception | Critical |
| Tracking Pixels | Privacy violation | Regulatory fines | Moderate |
| IoT Exploitation | Botnet recruitment | Resource abuse | High |
The convergence of these threats creates compounding risks. Initial reconnaissance using exposed IPs enables attackers to identify vulnerable systems, which then become entry points for credential theft or malware deployment. The breach cost report demonstrates how these multi-stage attacks drive up remediation expenses and regulatory penalties.
Pro Tip: Map your IP exposure to specific compliance requirements, documenting how each control addresses regulatory mandates to streamline audit processes and demonstrate due diligence.
Advanced persistent threats particularly leverage IP intelligence for long-term campaigns. By monitoring IP assignments and network changes over time, attackers identify infrastructure upgrades, mergers, or security programme gaps. This strategic reconnaissance informs timing and targeting decisions, increasing attack success rates. The research on IoT and NAT IP exploitation reveals how attackers chain multiple techniques to bypass defences.
Protect your IP information with instant IP lookup tools
Understanding your IP exposure is the foundation of effective protection. Instant IP Lookup provides comprehensive tools enabling you to assess and manage IP information proactively.
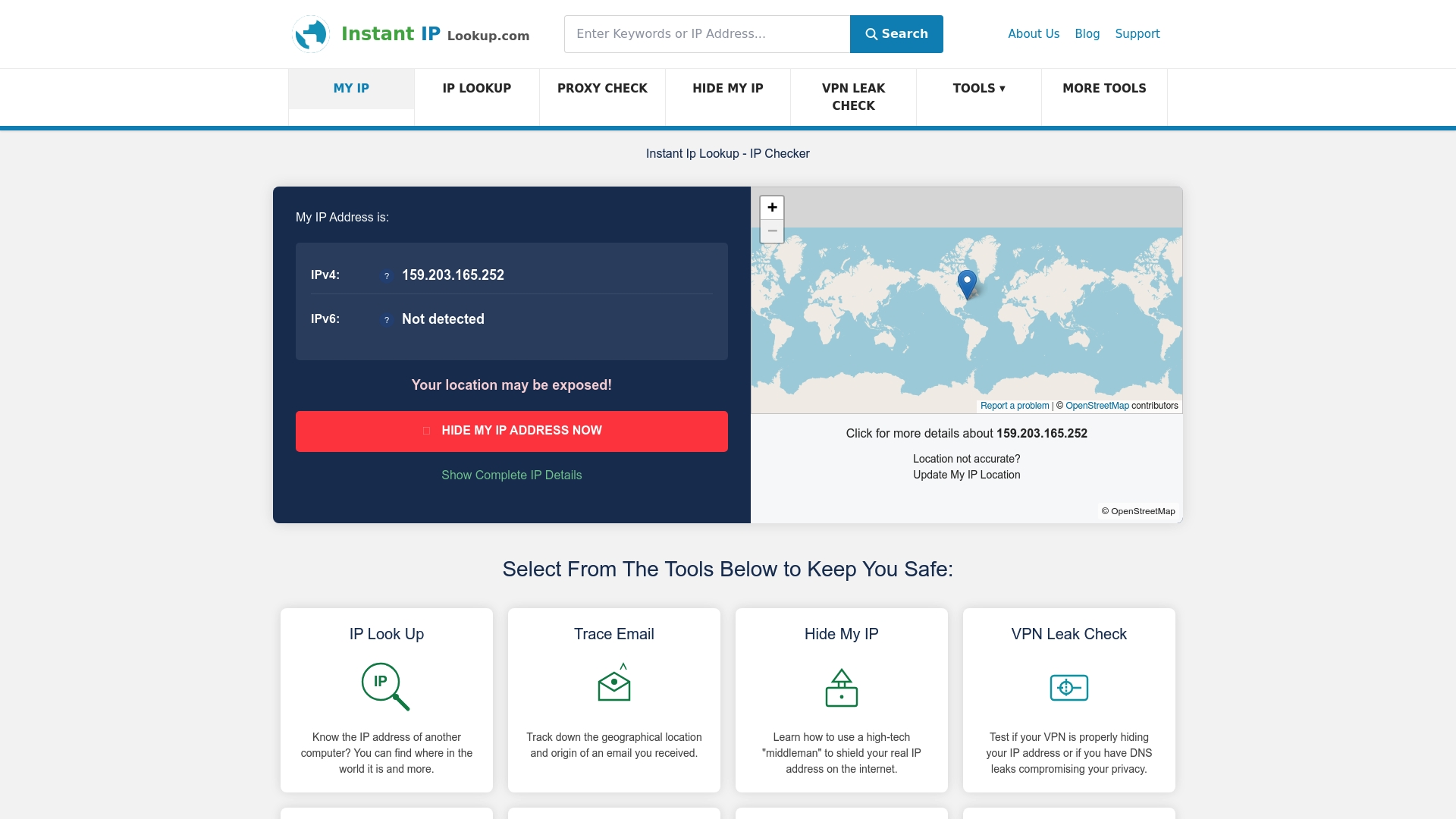
Our IP address lookup service reveals exactly what information your network infrastructure exposes, including geolocation data, ISP details, and potential vulnerabilities. The IP to location finder demonstrates how attackers correlate IP addresses with physical locations, helping you evaluate privacy risks. For teams implementing protection strategies, our digital footprint protection tools integrate seamlessly with existing security measures, providing real-time visibility into IP exposure across your infrastructure. These resources empower cybersecurity professionals to make informed decisions about network architecture and access controls.
Frequently asked questions about IP information protection
How do exposed IP addresses enable different cyberattacks?
Exposed IPs facilitate DDoS attacks by providing targets for traffic floods, enable IP spoofing for impersonation attacks, and allow port scanning to identify vulnerable services. Attackers also leverage IP information for BGP hijacking to redirect traffic and reconnaissance to map network topology before launching sophisticated intrusions.
Why does IP truncation fail to satisfy GDPR anonymisation requirements?
IP truncation remains reversible when combined with metadata like timestamps and user agents, allowing reidentification of individuals. GDPR requires anonymisation to be irreversible, meaning the data subject cannot be identified directly or indirectly. Truncated IPs paired with session data often enable correlation attacks that reconstruct user identities.
What emerging threats exploit IP information in IoT environments?
Compromised IoT devices serve as proxies for credential stuffing attacks, obscuring attacker origins whilst leveraging residential IP addresses to bypass security controls. Attackers also exploit IoT vulnerabilities to recruit devices into botnets for DDoS campaigns and use NAT traversal techniques to infer private IP addressing for lateral movement within networks.
How does IP encryption differ from traditional anonymisation methods?
Cryptographic IP encryption like IPCrypt transforms addresses using encryption keys whilst preserving network operations, unlike truncation which simply removes data. Encrypted IPs support analytics and troubleshooting without exposing raw addresses, offering strong privacy guarantees that withstand correlation attacks. The approach integrates with zero-trust architectures and maintains compliance with data protection regulations.
What role do IP addresses play in healthcare data breaches?
Third-party tracking pixels on patient portals transmit IP addresses alongside protected health information to advertising networks, creating HIPAA violations. These disclosures enable tracking of patient behaviour and correlation with medical conditions. Additionally, exposed healthcare network IPs facilitate targeted ransomware attacks, with attackers using IP reconnaissance to identify valuable targets and vulnerable systems before launching campaigns.

Comments (0)